Online Courses Catalog
Explore thousands of online courses from MIT, Harvard, Princeton and more — free and paid, self-paced or instructor-led.
25,649 courses available
25,649 results — page 189 of 1069

Fundamentals of Building Information Modeling
Purdue University
Learn the fundamentals of building information modeling (BIM), including object-oriented modeling, parametric modeling, and central database.
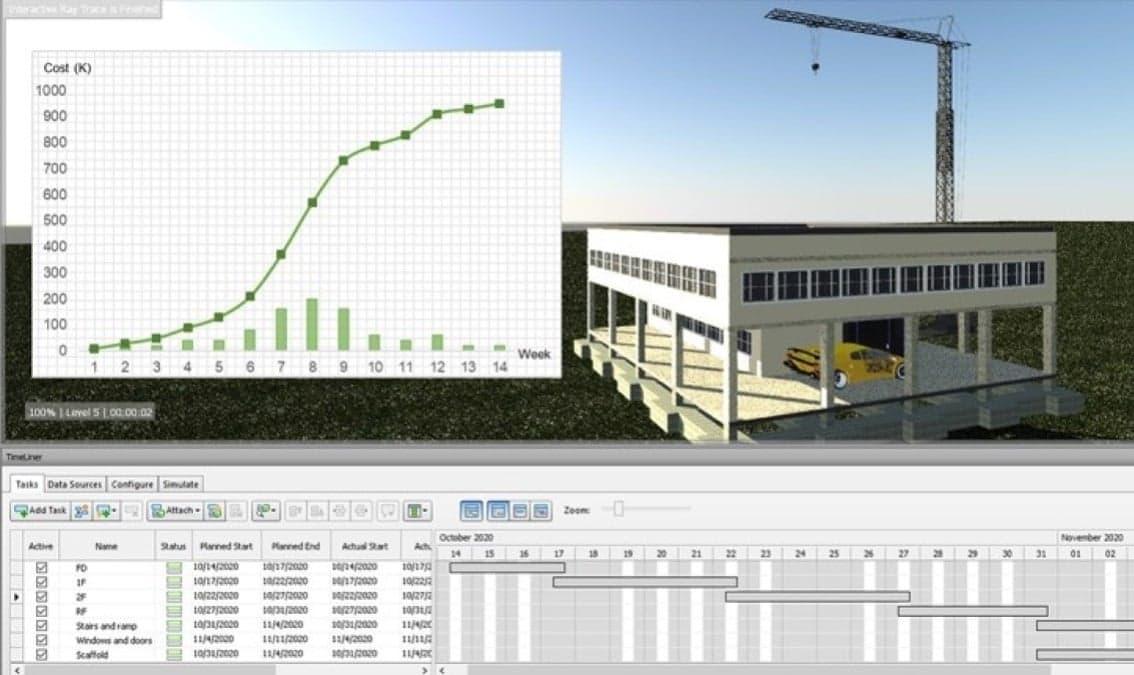
BIM for Construction
Purdue University
Learn how to couple BIM and traditional scheduling and cost-estimating tools to develop 4D, 5D, and nD models for effective construction applications

Metodologías disruptivas aplicadas a la industria de la Construcción, Arquitectura e Ingeniería (AECO)
Pontificia Universidad Javeriana
Aprende a utilizar las nuevas herramientas tecnológicas de la Industria 4.0 para optimizar cada etapa de tus proyectos de arquitectura, ingeniería, construcción y operación (AECO), ayudándote así a tomar las mejores decisiones dentro de un entorno digital .

Evolución tecnológica en la industria de la Construcción, Arquitectura e Ingeniería (AECO)
Pontificia Universidad Javeriana
Aprenda acerca de la evolución de las tecnologías en la industria de la arquitectura, ingeniería y construcción. Conozca el ecosistema digital al que nos enfrentamos en la construcción 4.0 y su relación con la cadena de valor en proyectos de esta industria.

Conflict Management: Mediation
Université catholique de Louvain
Learn the fundamentals of mediation as a conflict management strategy to effectively help others address their own conflicts.

Introduction to Conflict Management
Université catholique de Louvain
Learn the fundamentals about the psychological aspects of conflicts, get acquainted to conflict management strategies and identify your own conflict style.

Conflict Management: Negotiation
Université catholique de Louvain
Learn the fundamentals of negotiation as a conflict management strategy and identify the strategies that will lead you to optimal outcomes and negotiation success.

Managing Conflicts on Projects with Cultural and Emotional Intelligence
The University of Maryland, College Park
Great program managers understand and heal bad communication habits and conflicts that arise within project teams and stakeholders. Learn how by leveraging emotional and cultural intelligence using the Coordinated Management of Meaning (CMM).
Conflict Resolution
State Bank of India
It is no secret that conflict is a part of life and definitely a part of day-to-day business. Conflicts arise due to differences in personality or values. Conflict can be healthy. It is a perfectly normal and natural phenomenon of the human condition. Avoiding conflict can be termed as next to impossible. Therefore, learning how to handle conflict is central to build and maintain all relationships.

Managing conflict and polarization in the workplace and beyond
Jesus College, Cambridge
We all form groups. Sometimes they help us, other times they stimulate harmful or even violent polarization. Using expertise from business, behavioral science, and politics, we explore these ‘groupish’ instincts, while providing skills to bridge divides.

La gestion des conflits
HEC Montréal
En tant que gestionnaire, apprenez à cerner le noeud d’un conflit pour intervenir de façon adéquate et prévenir la résurgence des conflits.
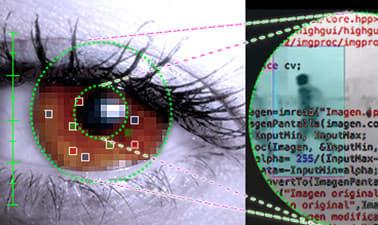
Introducción a la visión por computador: desarrollo de aplicaciones con OpenCV.
Universidad Carlos III de Madrid
Hasta dónde pueden ver las máquinas? Descubre la visión por computador programando aplicaciones de análisis de imágenes, uno de los campos más innovadores de la inteligencia artificial.

Transient-Execution Attacks: Understanding Meltdown and Spectre
Graz University of Technology
Beyond software-based side-channel attacks there is a new class of attacks called transient-execution attacks. These attacks go beyond leaking meta-data and directly retrieve secret data but they use side channels as an data exfiltration mechanism to transmit the secret data to an attacker-controlled application. We will look at the most prominent of these attacks: Meltdown, Spectre, Foreshadow, and ZombieLoad. You will implement some of these attacks yourself and learn how to mitigate them.

Web Security Fundamentals
KU Leuven
Essential knowledge for every web developer, discover important principles of modern web security, and learn about current security best practices.

Introduction to Software Side Channels and Mitigations
Graz University of Technology
Side channels exist in the real world, but they also exist in computers and can be exploited directly from software. This is a substantial computer security problem today, that we need to learn about to be able to stop attacks. In this course, you will learn and practice basic software-based side channels and understand the thought process to utilize a side channel. You will then learn how to mitigate or avoid side channels in software.

Cache Side-Channel Attacks and Mitigations
Graz University of Technology
Software-based side-channel attacks can pose a severe security threat in practice. In this course, we focus on a particularly prominent case: caches and cache side-channel attacks and we will go beyond the basic Flush+Reload attack. You will work with different cache side channels and understand where timing differences in architectures originate. You will learn which mechanisms can mitigate specific side-channel techniques in practice.
Introduction to dApp Development with Solana AnchorLang
Xccelerate
Master Blockchain principles, Encryption techniques and the art of developing smart contracts. Unlock new opportunities for your career in Smart Contract and dApp Development.
Smart Contract and Solana dApps Development with Rust
Xccelerate
Master blockchain principles and smart contract development using Rust on Solana. Designed for those with programming experience, this course unlocks new career opportunities in Smart Contract and dApp Development.

Unsupervised Learning
University of Maryland Baltimore County
Unsupervised learning is a category of machine learning algorithms that use unlabeled data and no prior training. Many algorithms fall into this category. This class will cover the more popular ones of K-Means, DBSCAN and Hierarchical Clustering. The course ends with a capstone project.

Next-Gen Security: Mobile, IoT, and Cloud
University of Maryland Baltimore County
This course introduces wireless transmission, attacks on wireless transmission, and defenses against these attacks. It also introduces the concept of Cloud security.